Trendingnow
Cybersecurity

By Emma Burrows and The Associated PressMay 30, 2026
Latest Stories
More CybersecurityPage 22 of 100

SuccessKevin Mitnick, the world’s ‘most wanted’ hacker before becoming a cybersecurity consultant, dies at 59
By Chris MorrisJuly 20, 2023

By David MeyerJuly 18, 2023

PoliticsSensitive U.S. military information has been sent to Mali for years thanks to a simple typo. Now the Russia-friendly government will get access to it
By Chloe TaylorJuly 17, 2023

By Leo SchwartzJuly 11, 2023

By David MeyerJune 28, 2023

By Frank Bajak and The Associated PressJune 18, 2023

By The Associated PressJune 16, 2023

By Christiaan HetznerJune 16, 2023
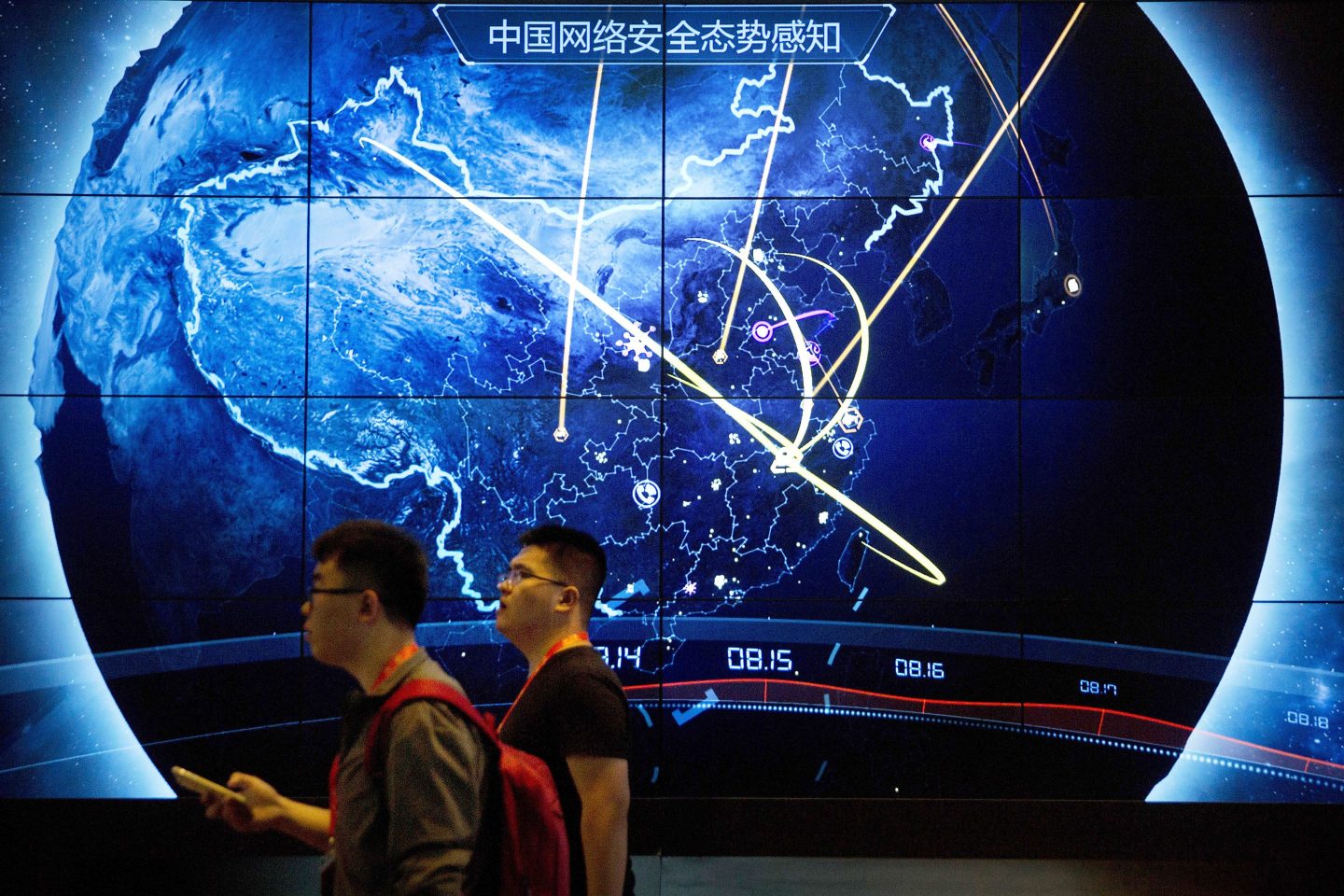
CybersecurityGoogle claims it caught China government hackers redhanded breaking into hundreds of networks around the world
By Frank Bajak and The Associated PressJune 15, 2023

CybersecurityChina-backed hacker group called ‘Volt Typhoon’ has been working to cripple American infrastructure, Microsoft says
By Frank Bajak and The Associated PressMay 25, 2023

NewslettersSentinelOne CEO Tomer Weingarten has been building an A.I.-powered cybersecurity firm for a decade
By Lucy BrewsterMay 19, 2023
By Richard Forno and The ConversationMay 12, 2023

By Lila MacLellanMay 10, 2023

LifestyleFBI and FCC warn Americans over ‘juice jacking’ at public phone charging stations: ‘Don’t let a free USB charge drain your bank account’
By Chloe TaylorApril 11, 2023

CompaniesCAT Labs, a crypto crime-fighting startup led by a former DOJ special agent, raises $4.3 million
By Leo SchwartzApril 11, 2023

NewslettersThe bombshell report that Tesla employees had access to cars’ video recordings is a reminder of a risk we all face
By Kylie RobisonApril 7, 2023

NewslettersThe tale of a stalled ski resort explodes the myth that founders don’t need outsiders on their boards
By Lila MacLellanApril 7, 2023

LeadershipScience academy principal quits after she tried to hand over $100,000 in school funds to a fake Elon Musk
By Chloe TaylorApril 3, 2023

By Lila MacLellanMarch 31, 2023

The CoinsMassive vulnerabilities revealed at Dogecoin, Litecoin, and Zcash, with developers warning of additional risks
By Leo SchwartzMarch 13, 2023

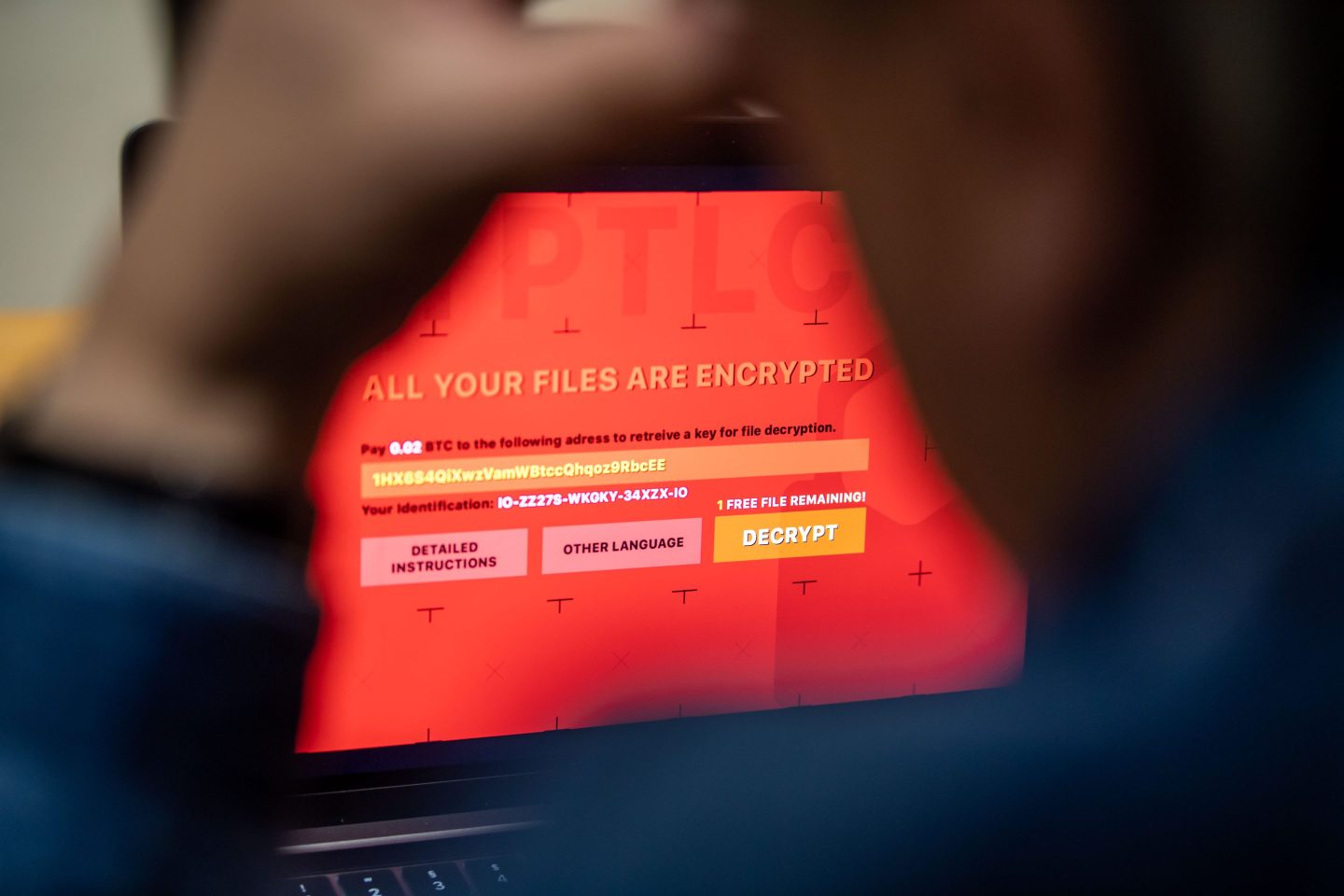
TechMicrosoft and Twitter’s protections against ransomware attacks are ‘disappointing,’ U.S. cyber chief says
By Katrina Manson and BloombergFebruary 27, 2023

By Lucy BrewsterFebruary 15, 2023
CommentaryThe cost of cybersecurity insurance is soaring–and state-backed attacks will be harder to cover. It’s time for companies to take threats more seriously
By Shmulik YehezkelFebruary 15, 2023

TechChatGPT lets scammers craft emails that are so convincing they can get cash from victims without even relying on malware
By Jeremy KahnFebruary 3, 2023

By Alice HearingJanuary 23, 2023

By Brad HaftJanuary 11, 2023
Most Popular