Two years ago when Rob Lee first sought funding for his cybersecurity startup Dragos, most venture capitalists didn’t deem the business “investible,” he says.
The market for securing industrial control systems—machinery used in manufacturing, water treatment, power plants, and oil and gas facilities—struck prospective backers as too complex, slow-moving, and small. The opportunity wasn’t obvious, even in the immediate aftermath of a hacker-induced outage of a Ukrainian power grid by a group associated with Russia in December 2015.
Today Dragos is having no such difficulty. The Hanover, Md.-based firm, which employs more than 80 people, said Wednesday it raised $37 million in new venture capital. The company has raised a total of $48 million in three rounds of funding to date.
Knock-down, Dragos
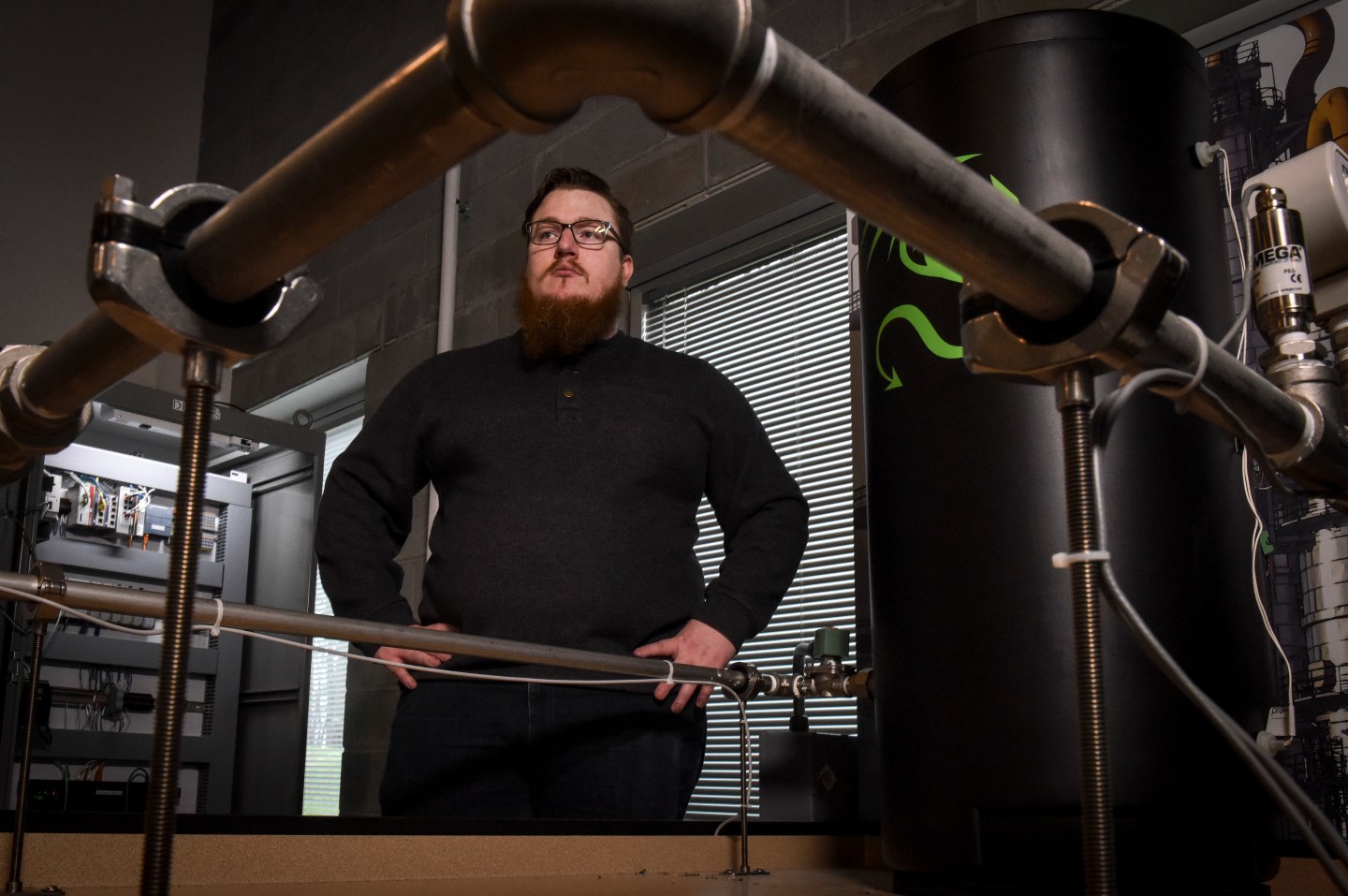
Lee helped defend critical infrastructure and scout out global threats while serving at the National Security Agency and U.S. Cyber Command between 2011 and 2015. A year later, he left the public sector to cofound Dragos with two former NSA colleagues, Jon Lavender and Justin Cavinee.

Since forming Dragos, Lee and his team have been tracking eight nation state-sponsored groups of attackers that are actively targeting industrial systems. This includes the makers of “crash override,” a piece of power-squelching malware that took part of Kiev’s energy grid offline for about an hour in 2016.
Dragos also discovered, alongside FireEye, a rival cybersecurity firm, an industrial safety system-subverting attack it dubbed “Trisis.” If the malware in question had worked as (presumably) intended—causing high pressure systems at a petrochemical plant in Saudi Arabia to malfunction—the attack could have claimed lives.
“There’s no gray area,” Lee said on a call with Fortune. “If you’re in someone else’s industrial environment, you’re the bad guy.”
Lee said his firm does not publicly identify the provenance of the threats it tracks and discovers, preferring to focus solely on booting them off customers’ systems. The policy runs counter to the prevailing approach among Dragos’ peers in the threat intelligence market, such as FireEye, CrowdStrike, and Kaspersky Labs.
“We don’t do attribution,” Lee said, while noting that his firm does provide tip-offs to various governments.
“It’s not important for our customers,” Lee said. As far as the threat actors are concerned, he continued, “we’re focused on finding them and kicking them out of those environments.”
Powering up
Canaan Partners, a U.S.-based venture capital firm, led Dragos’ new funding round, putting up $21 million. Existing investors—Energy Impact Partners, AllegisCyber, and DataTribe—contributed another $15 million. The remaining $1 million was split between strategic backers in the industrial sector, including Emerson, Schweitzer Engineering Labs, and the newly formed venture capital arm of National Grid.
Bob Yeager, president of power and water solutions at Emerson, told Fortune that his company invested in Dragos because the industry as a whole is under fire from hackers like never before. “Attacks are increasing significantly,” he said. “There are many large state-sponsored groups that, when they come into work every day, their job is to try to penetrate other countries.”
Lisa Lambert, who leads technology and innovation at National Grid, agreed. She said National Grid had been receiving threat intelligence reports from Dragos for some time, but is now exploring deepening the relationship by signing up for Dragos’ intrusion detection services, which alert industrial operators when their systems may have been breached and advise them on how to react.
Dragos’ rivals in the industrial control systems security market include Claroty, CyberX, Nozomi Networks, Radiflow, SCADAfence, and SecurityMatters, the last of which was just acquired by cybersecurity firm ForeScout for $113 million.
Joydeep Bhattacharyya, the Canaan partner who led Dragos’ new investment round, said that while he initially considered the industrial security market not to be an investment opportunity, a confluence of factors changed his mind over the past year or so. Chief among them: the exposure of multiple high-profile malware campaigns targeting industrial systems and a newfound interest from C-Suite executives at industrial companies in overhauling their operational technology systems.
Bhattacharyya, whose father worked for industrial tech maker ABB, said that Lee’s tenure at NSA and his experience teaching industrial control systems security at the SANS Institute, a cybersecurity training organization, made backing Dragos an easy choice for him.
“All these guys running security who are key in the industry, they are basically Rob’s students of the last 10 years,” he said.