In the world of digital thievery, a business model pivot is apparently underway.
Over the past year cybercriminals have shifted their focus from ransomware attacks to so-called cryptojacking. That’s the marquee finding out of a new threat report published by IBM this week: Instances of the former money-making scheme were down 45% in 2018, while occurrences of the latter surged 450% in the same timespan, per IBM’s data.
Whereas with ransomware, hackers were locking up victims’ computer files and reinstating access only after being paid a ransom, cryptojacking has involved hijacking people’s computers to “mine,” or run programs that produce, cryptocurrency. These mining scams have been caught everywhere from websites of the U.S. court system, to Google Chrome extensions, to Tesla’s cloud-computing infrastructure, and beyond.
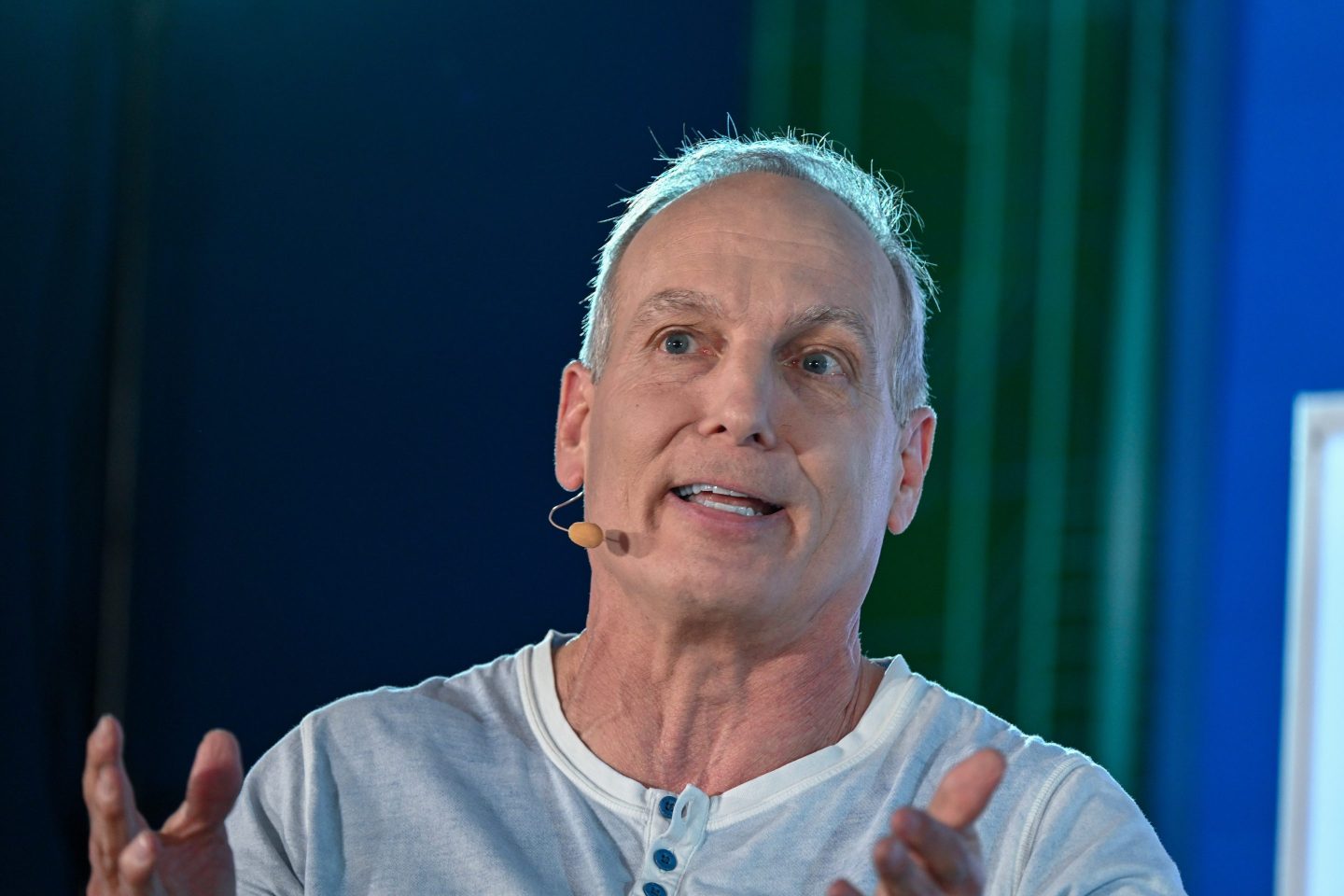
I spoke about the implications of the trend with Charles Henderson, who leads the hacking team that produced the research, IBM’s X-Force Red. (“I like to tell people that X-Force Red is a new shade of IBM blue,” Henderson says, with a touch of Texas drawl, of his not yet 3-year-old unit.)
Henderson views the criminal underground’s turn toward cryptojacking as a bit of fine-tuning in the quest for profits. “This isn’t the Olympics, there are no style points…there are no sharks with lasers on their heads,” Henderson says. Instead of pursuing fancy hacking flourishes, criminals are interested solely in the easiest path to ROI, or return on investment, he says.
Because cryptomining is less disruptive to consumers and businesses than extortion, it’s a sounder means of generating revenues. “With the extortion racket of ransomware, you lose the customer after one transaction, so it’s a one and done, there’s no recurring revenue—I mean its just bad business,” Henderson says.
Now the baddies have wisened up; they’ve learned the budgetary benefits of regularity and predictability. “The bane of any founder is that chunky revenue stream,” Henderson says, referring to the inconsistency of one-off ransom payments. The mining model, on the other hand, has all the advantages of subscription revenues.
One troublesome outcome of this change in tactics is that cybercriminal attacks are flying under the radar more often. “When you have a screen staring you in the face that says it’s not going to give your files back unless you pay, that is a Level One emergency,” Henderson says. But if you merely hear some complaints about slower-than-usual Internet connection speeds, as may be the case for victims of cryptojacking, that raises fewer alarms.
Ignoring this ballooning threat is, ultimately, a big mistake; the scheme could wreak considerable havoc down the road. “The criminals are setting themselves up for future expansion of their criminal enterprises,” Henderson warns.
Indeed, what consists of stealthy cryptocurrency mining today could easily evolve into schemes for cracking troves of hashed, stolen passwords for all sorts of nefarious purposes in the future. Afflicted machines could become a springboard for launching more insidious attacks. And the cryptojackers could even sell the botnets they amass to threat actors with far worse intentions.
Crime is a business, and the crooks are studying, mastering, adapting at a rapid clip. “It’s like the criminals went to ‘B’ school,” Henderson says.
Robert Hackett
@rhhackett
robert.hackett@fortune.com
Welcome to the Cyber Saturday edition of Data Sheet, Fortune’s daily tech newsletter. Fortune reporter Robert Hackett here. You may reach Robert Hackett via Twitter, Cryptocat, Jabber (see OTR fingerprint on my about.me), PGP encrypted email (see public key on my Keybase.io), Wickr, Signal, or however you (securely) prefer. Feedback welcome.
THREATS
The empire strikes back. U.S. Cyber Command disrupted potential interference campaigns by Russia's Internet Research Agency during last year's midterm elections, reports the Washington Post. "They basically took the IRA offline," one source told the Post. CyberCom is flexing its muscles after being imbued with new powers to take offensive action below the level of armed conflict. The national security blog Lawfare wonders, however, whether the Kremlin may be saving its best efforts for the 2020 presidential election.
Chinese finger traps. Two divisions within Huawei pleaded not guilty in a federal court to stealing intellectual property from telecom giant T-Mobile. The pleas follow last month's unsealing of an indictment in the U.S. that alleged, in part, that the Huawei units had tried to steal trade secrets related to a T-Mobile robot, called Tappy, designed to simulate human touch on smartphones. Meanwhile, the Federal Trade Commission fined TikTok, formerly known as Musical.ly, a video app owned by China's Bytedance, for illegally collecting children's data.
Russian spy games. A Moscow court sentenced two people—a former cyber intelligence chief and a former executive at cybersecurity firm Kaspersky Lab—to decades in prison on charges of treason. The proceedings occurred behind closed doors, and the details of the case remain unclear—though rumors have floated that it might have involved passing along confidential information related to Russian interference in the 2016 U.S. presidential election. In other news, the daughter of Russian President Vladimir Putin's spokesperson has been working as an intern in the European Parliament.
Let's chat. The Wall Street Journal quizzed Steve Bellovin, a computer science professor at Columbia, about the privacy implications of 5G technology, which he says will enable mobile carriers to "know much more precisely where you are." Recode spoke to Matthew Gentzkow, a Stanford economics professor, about his recent research into how unplugging from Facebook affects people: "The healthiest settings in which news and politics content can be consumed need to have a substantial element" of human curation, he says. (At Fortune, we agree.)
Who wants to be a millionaire?
Share today's Cyber Saturday with a friend:
http://fortune.com/newsletter/cybersaturday/
Looking for previous Data Sheets? Click here
ACCESS GRANTED
"No, data is not the new oil." So says Antonio García Martínez, a Wired contributor who headed Facebook's early ad-targeting team. In Martínez's view, all this talk about tech giants paying a dividend to users as compensation for their data makes no sense. What works in Alaska—where residents receive a yearly payout for the petroleum extracted within the state—will not work in the digital marketing industry, he argues.
Ultimately, the majors like Google and Facebook will raise the castle walls around their data (and users) and disclaim any knowledge of data brokering, the “data-as-oil” traders. It’ll be first-party data all around: Publishers, apps, and ecommerce all huddling around their data and user piles, projecting that data externally in data-safe ways if absolutely necessary, but not otherwise.
No, data isn’t the new oil. And it never will be, because the biggest data repositories don’t want it to be.
FORTUNE RECON
One in Five U.S. Companies Say China Has Stolen Their Intellectual Property by Erik Sherman
KKR Invests in Cybersecurity Firm KnowBe4 at $800M Valuation by Rey Mashayekhi
California Was on Everyone's Mind at Congressional Data Privacy Hearings. Here's Why by Danielle Abril
YouTube Hopes to Silence Child Predators by Shuttering Comments on Videos of Kids by Alyssa Newcomb
How Huawei Is Battling U.S. Spying Allegations by Aaron Pressman
Google, Facebook, and Apple Are Fighting International Regulators to Keep User Data Private by Don Reisinger
ONE MORE THING
I, Robot. Ever wonder why bots can't check those simple "I am not a robot" boxes Google uses across the web? What may appear to be a simple action—checking a box—is undergirded by a panoply of anti-bot measures. That unassuming square has a virtual machine, or simulated computer within a computer, behind it, which uses a specially encrypted programming language, challenges in the form of invisible coded images with nonsense fonts, and reviews of browser fingerprints alongside people's web search history to figure out whether a visitor is real.