Researchers at the Citizen Lab, an Internet watchdog group based at the University of Toronto, published a deep dive on Monday about a seven-year hacking campaign against South American political dissidents, journalists, and others. During the investigation, the cyber spies engaged with the researchers directly, issuing a series of taunts, jabs, and threats on the screens of their infected machines.
“We are going to analyze your brain with a bullet and your family too,” one attacker said in Spanish in a pop-up window that appeared on a researcher’s computer screen. (Original: “Vamos a analizar tu cerebro con una bala y en la de tu famila.”)
Other admonitions appeared, too. “You like playing the spy where you shouldn’t, you know it has a cost: your life!” another warning read, translated here into English. “We have your picture,” “Take care of your family,” and “You think you’re living, we have your IP!”
Menacing exclamations occasionally played aloud through the team’s computer speakers. (The hackers may have been “aiming for surprise value,” the researchers speculated.) Some threats arrived in broken English. For example: “We gou You Punk!!” and “Your are playing with fire, will get burn!”
The hacking group—dubbed by the researchers as “packrat” for its use of certain hacking tools (remote access trojans, or RATs) designed to infect devices, monitor their users, and evade detection by anti-virus software—did not appear to be highly sophisticated. The hackers relied on off-the-shelf digital spying tools such as AlienSpy, Adzok, Cybergate, and Xtreme, without implementing technically sophisticated exploits. But that did not mean they should be simply disregarded.
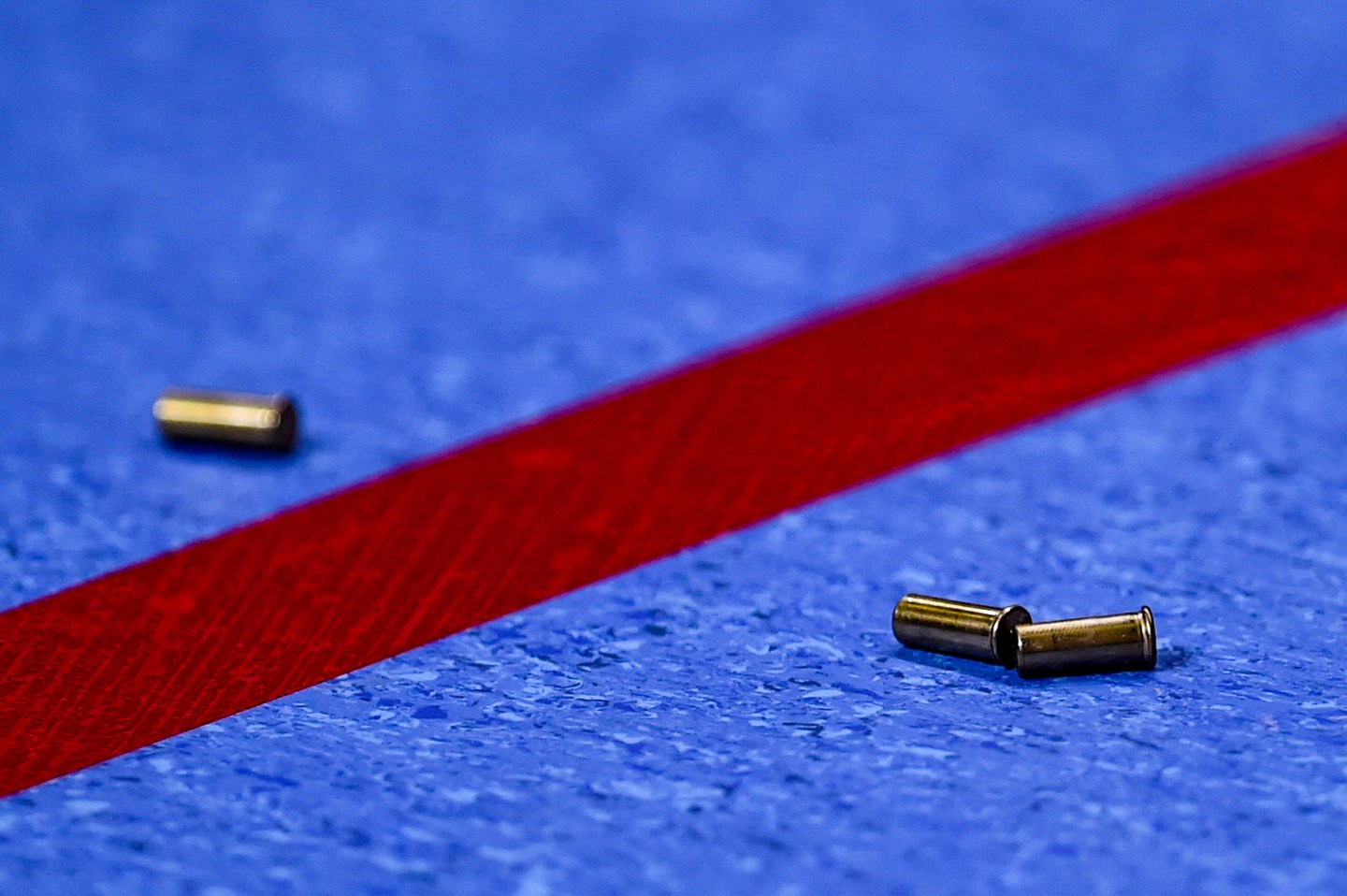
Security researchers began investigating the group after discovering that Alberto Nisman, a prominent Argentinian lawyer, had been targeted by the gang’s spyware shortly before he was found dead in his apartment. He had been shot in the head the night prior to his scheduled testimony before the country’s Congress about a possible conspiracy involving its president, Cristina Fernández de Kirchner, and other government officials. The correlation between the spyware and his death is compelling, though not conclusive.
Interestingly, the packrat group didn’t seem to mind being discovered by Citizen Lab. The hackers consistently reused the same domains and infrastructure to wage cyberattacks, even after parts of that infrastructure had been exposed. Perhaps they did not fear reprisal from law enforcement, the researchers surmised.
By all indications, the group appeared to be a state sponsored outfit, the researchers noted. Its targets included political opposition leaders in countries such as Ecuador, Venezuela, Brazil, and Argentina. The researchers consider the state actor scenario to be “most likely,” for a number of reasons, including its political bent, although they stopped short of definitively attributing the attacks to a government-backed team. (The researchers made a point to leave open the possibility that the hackers could represent a mercenary organization, a well-funded group with political aspirations, or a criminal gang with ties to cartels or illegal traffickers.) Notably, the cyber espionage group behaved in a less expert and more careless manner than the world’s top hacking powers.
Alex Stamos, security chief at Facebook, observed this in a post on Twitter. He, for one, is well-acquainted with state-sponsored cyberattacks; a notification tool the social network rolled out this year recently alerted the U.S. State Department that officials’ online accounts had been compromised, allegedly by Iranian hackers according to the New York Times.
https://twitter.com/alexstamos/status/674460255883948032
The researchers were unable to definitively prove the identities of the hackers with the information they had. But there is a case to be made, supported by the attackers’ methods, their focus on dissidents, and their brazen activity, that one or more governments, probably South American, are behind the group.
Read the full Citizen Lab report here.
Follow Robert Hackett on Twitter at @rhhackett. Read his cybersecurity, technology, and business coverage here. And subscribe to Data Sheet, Fortune’s daily newsletter on the business of technology, where he writes a weekend column.
For more about hackers, watch the video below: