The U.S. is less than a year out from one of the most consequential elections of the century, which President Donald Trump’s Department of Homeland Security has called “the big game” for foreign adversaries looking to attack and undermine the Democratic process. Congress, meanwhile, is locked in a stalemate about how to secure systems in the country’s 8,000 largely disjointed voting jurisdictions.
Tuesday marks the last test of security preparedness before the 2020 elections, as certain statewide polls take place around the country. The Department of Homeland Security is gearing up “war rooms” to monitor for potential interference and test voting infrastructure, but with sluggish movement at a federal level there is little they’ll be able to do to correct any issues within the next 12 months.
There is, however, one beacon of hope: 2002’s Help America Vote Act (HAVA)—a block grant issued to states to bolster election security following the Bush v. Gore hanging chad debacle some 19 years ago.
In 2018, Congress used the Omnibus Appropriations Act to pad HAVA with an extra $380 million to be divided up amongst the states in proportion to their voting age population. The idea was that they spend it to prepare for the 2020 elections, and Democrats and Republicans are likely to approve at least another $250 million through the act this year.
“We cannot sit on our hands while our adversaries – Iran, China, North Korea – try to replicate and out-do what Putin accomplished in 2016. Election officials—Democrat or Republican—throughout the country have made it clear that they need more money for election security,” Senator Minority Leader Chuck Schumer (D-N.Y.) told Fortune.
In order to receive the funds, each state submitted a plan to the U.S. Election Assistance Committee (Brian Newby, the agency’s former executive director, has been accused of blocking important election security protocol, causing the recent exodus of nine director-level employees). States are not, however, required to follow up with the committee to report how they actually spend the funds. Despite protests from advocates at election defense and security organizations, the committee has also declined to issue recommendations on how the states should spend their money to ensure best practices and guarantee the best results.
The EAC, an agency charged with creating a program for the testing and certifying voting systems and creating voluntary voting system guidelines, has not issued any public advice to states since their original 2002 guidelines to create statewide voting registration systems, make voting more accessible for disabled Americans, and update voting systems to avoid those hanging chad problems.
“From an election security perspective they have not adequately faced the election security threat that we’ve learned the severity of,” said Susan Greenhalgh, vice president of policy and programs for the National Election Defense Coalition, a bipartisan group charged with securing elections. “They have no regulatory authority or directorial authority to tell the states what to do, but they can articulate the risks of some insecure election practices.”
Greenhalgh called the understaffed organization a “hot mess.”
Earlier this year, Greenhalgh wrote a letter to the EAC detailing some simple suggestions, like explaining that voting online is unsafe (32 states still allow this practice for some citizens), or that there should be audits to ensure voting machines are safe. The letter has so far been ignored. “Their silence ends up being a message to the states,” she said.
There are multiple pieces of election security legislation that have been backed in the House but have died in Senate after they were blocked by Senate Majority Leader Mitch McConnell (R-Ky.), who prefers to give the states autonomy on election issues.
Schumer, for his part, doesn’t think that administering state funds without attached legislation will make an impact on election security. “What’s also clear is the need for legislation to ensure that the money is used in the most effective way possible,” he said. “If Congress only provides funds without meaningful policy guidance, the job will remain incomplete, and our democracy vulnerable.”
Still, all 50 states submitted their applications with a focus on election security, and the money has been administered.
“The 2018 HAVA Funds have been used to make a tangible difference in the efficiency, security, accessibility and integrity of American elections,” said EAC Chairwoman Christy McCormick in an April 2019 report that outlines how the money has been spent thus far.
The majority of states will spend the funds on five major categories: increasing cybersecurity, replacing and fixing voting equipment, updating voter registration systems, auditing elections, and communications.
Funding ranges from $3 million (Alaska, Delaware, Montana, Vermont, Rhode Island, and Wyoming) to $34.5 million (California) per state.
In total, states intend to use $136 million of the funding to strengthen election cybersecurity, $103 million for voting equipment, and $21 million on post-election audits.
Voting Equipment
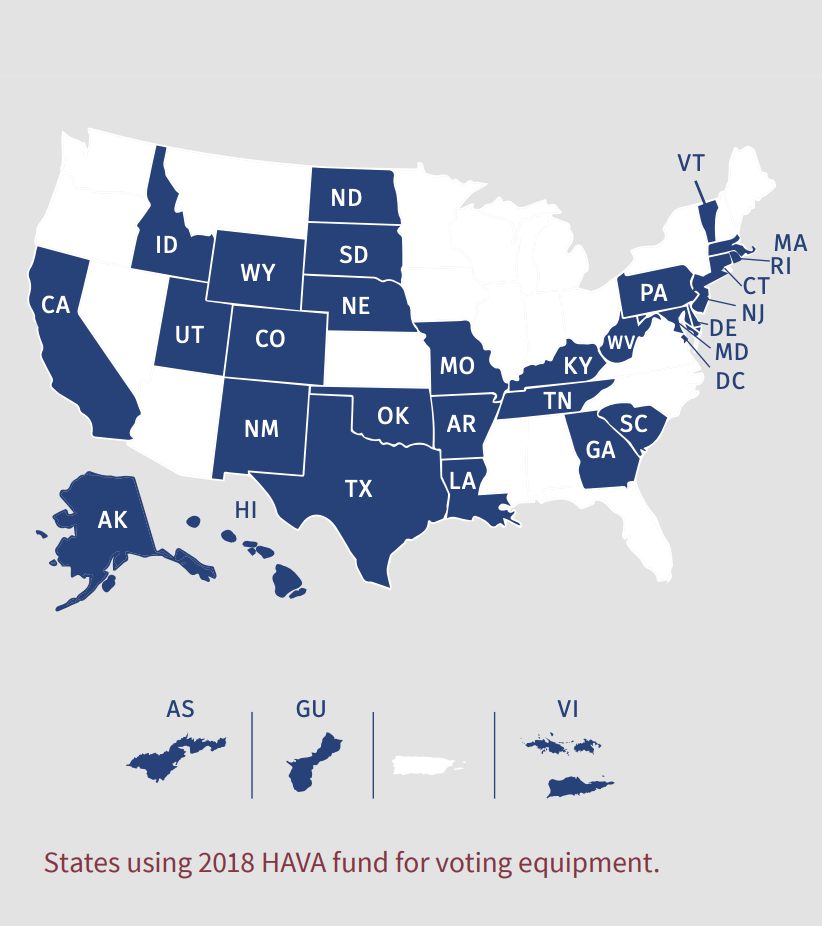
As of the 2018 midterm elections, 45 states were using voting equipment so old that it is no longer manufactured, and the vast majority of states will use some funding to replace or repair those machines. A recent study by the Brennan Center for Justice recorded 121 officials in 31 states who said they had to replace their equipment before the 2020 election.
What those states replace their systems with will make a big difference in election security. The intelligence committees in the U.S. Senate and House of Representatives, the National Academy of Sciences, and election security experts have all said that machines that don’t produce paper records of every vote create unnecessary security risks. President Donald Trump himself said in August that “going to good, old fashioned paper, in this modern age, is the best way to do it.”
But just six states—Arkansas, Delaware, Georgia, Kansas, North Dakota, and Pennsylvania—indicated in their filings that they would upgrade their systems to include voter verified paper backup (it’s possible that other states will upgrade to paper backup, but they did not specify).
Some states chose to ignore that security guidance. Some let decentralized voting districts pick which equipment to purchase. Others can’t afford to upgrade to paper, so they patch existing digital systems.
Certain jurisdictions may see paperless ballots as “fast, easy, cool and the newest thing,” said Eddie Perez, global director of technology of the non-partisan Open Source Election Technology Foundation (OSET), but they’re actually the opposite. These jurisdictions could find themselves in situations where the election is a close call and they have to go back and figure out voter intent. Without a paper trail, “they may have no way to recount, they may have no way to go back and audit that election.”
During the 2018 election, citizens of 36 states cast their votes on machines that used some form of paper ballot, many of which were just upgraded with printers. Texas, Florida, Pennsylvania, Delaware, Georgia, Louisiana, New Jersey, South Carolina, Indiana, Kentucky, Mississippi, Tennessee, and Arkansas were entirely paperless for the midterm elections.
With their HAVA funding, New Jersey will implement a Voter Verified Paper Audit Trail Pilot Program, which will let counties purchase or test new voting systems—but there will be no requirements to use them.
Schumer proposed a bill on the Senate floor to require backup paper ballots in election systems, but the proposal was blocked by McConnell.
“In 2017, even knowing everything that was known about foreign interference in the 2016 elections, there are jurisdictions in the U.S. that are buying brand new paperless devices, that’s the kind of thing we’re up against,” said John Sebes, co-founder and chief technology officer of OSET.
That’s if they can even afford the machines. Two-thirds of officials who told the Brennan Center for Justice that they needed to replace their voting machines before 2020 said they didn’t have the funding to do so, even with their HAVA grants. The Center estimates that the cost of replacing the remaining paperless Direct Recording Electronic voting machines in use in the United States would cost somewhere between $130 million and $400 million, not including associated costs.
Very few states explained how they planned to evaluate which machines to buy in their grant requests, which could also cause security problems, said Greenhalgh.
“Just giving the states money through the appropriations process without any specific accountability guidelines will just going to create more problems,” she said. “Right now there is very little regulation and oversight into the voting system industry, all we have is a voluntary standard that was written in 2005 that voting machine vendors don’t have to adhere to.”
Greenhalgh also worries about disinformation about voting machines and internet connectivity. She says she often hears election officials say machines that aren’t directly connected to the internet can’t get hacked, which disincentivises the use of paper machines or election audits.
“All of these systems are programmed by another device, and that device is generally a laptop computer that sits on the internet and if that machine is hacked then the voting machines are hacked,” she said.
Cybersecurity
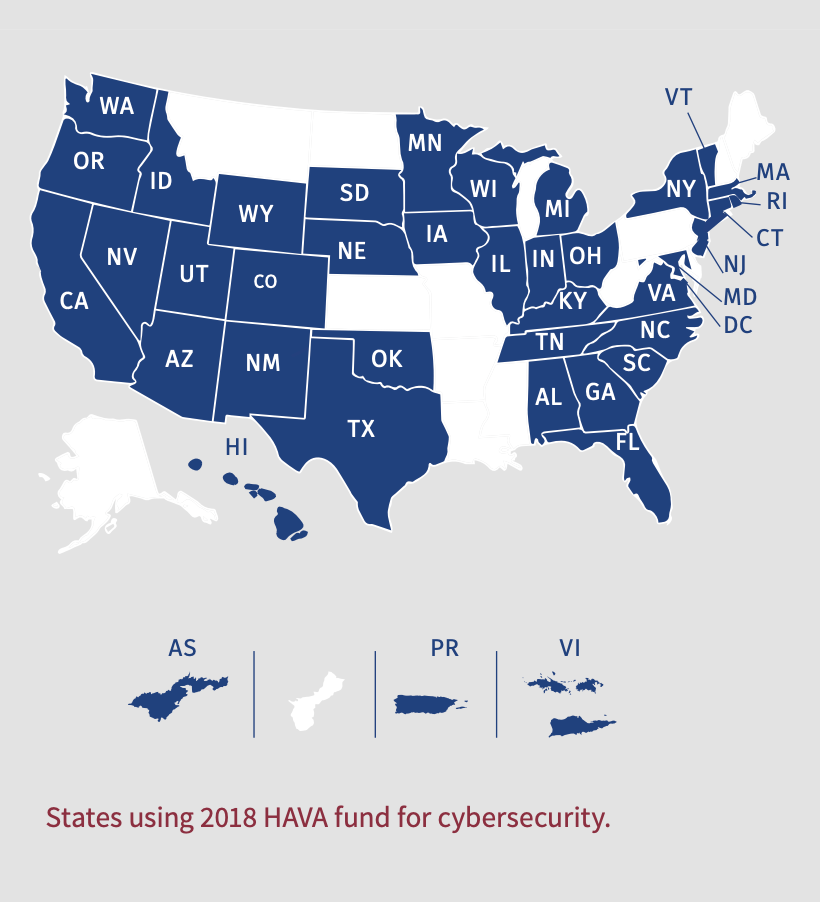
That disinformation is likely why the majority of states also plan to train their employees on cybersecurity threats.
“It’s important for every employee at a local election office to get trained on what phishing is, don’t open any email attachments and all that stuff, but that doesn’t necessarily mean that it’s the most effective way of spending that money with respect to the threats that they face,” said Sebes. It may also be too little too late. “Basic training for staff is a drop in a very large bucket,” he said.
Some states are going beyond basic training and using funds to hire experts in election security and tech.
Hawaii plans to hire an election information specialist; Illinois will hire someone they’re referring to as a cyber navigator/adviser; Massachusetts has hired a network security engineer; and New Mexico hired an IT security and compliance administrator “whose responsibilities include implementing additional security practices to safeguard sensitive data and election systems and protect against cyber vulnerabilities.” North Carolina will bring on a chief information security officer and also create a cyber advisory panel.
It’s largely unclear what qualifications are needed for these roles and how large of a part they’ll play in upcoming elections.
The state grant applications were likely vague on purpose, said Sebes.
“Some people would regard cybersecurity initiatives, wrongly in my view, as confidential. They think they’re revealing to the bad guy what defenses they’re building.”
Instead, he explained, they create a lack of awareness and communication about what different states are doing to protect their elections. What does become apparent in the filings is how behind certain states are.
At least three states—Indiana, Iowa, and Maryland—noted that they would implement two-factor authentication to help protect their elections, the same type of security many Americans use to protect their email and social media accounts.
“You can say that’s good, but also isn’t it a shame to say that barely a year before a federal presidential election, knowing about the threat environment, states are just now getting two-factor authentication?” asked Perez. “It’s a much overdo minimum, the equivalent of a seatbelt.”
Most of the election technology currently being deployed, Perez said, is still set back by about 14 years, “and there is a tremendous amount of inertia in the commercial environment in the face of change.”
Local election officials “are being completely swamped with a gazillion offers for different kinds of cybersecurity products and services and not really clear on what they need or should be doing,” said Gregory Miller, chief operating officer at OSET.
Forty-one states will use funding to implement some new form of cybersecurity.
Voter Registration
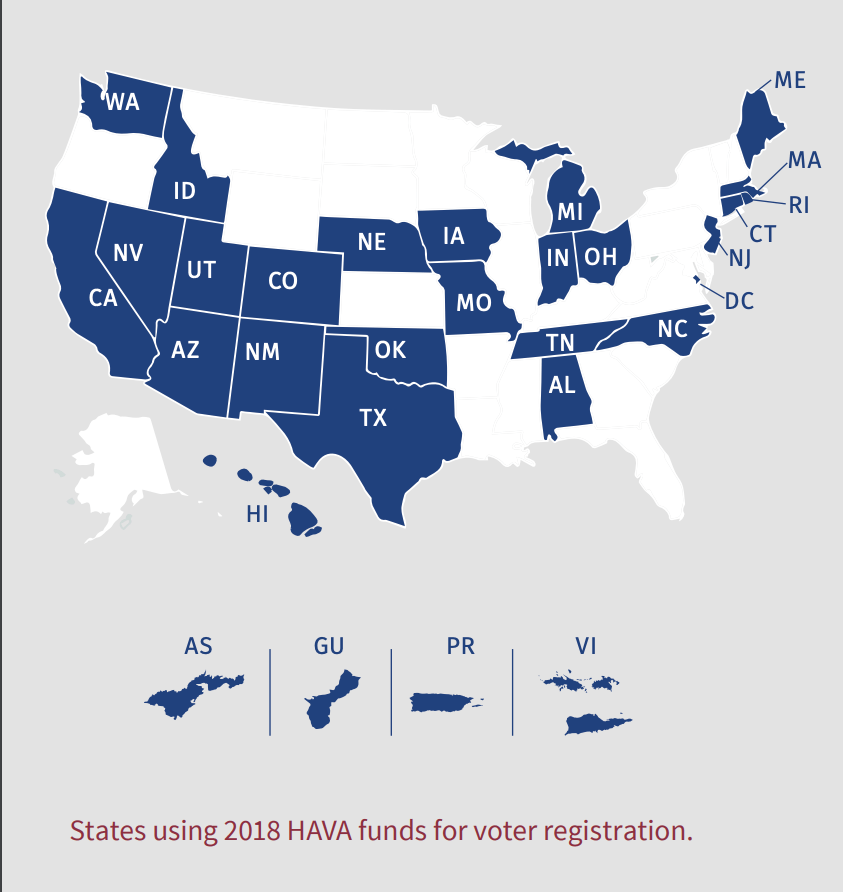
Concerns about voter registration and registration security are often overshadowed by fear about election systems, but they’re often just as important and an easier utility to upgrade immediately ahead of an election, said Perez.
“At this point in the calendar, time is up for any significant movements in deployed voting technology. That’s not going to happen,” he said. “But voter registration systems can still be tended to.”
At least 18 voter registration databases were scanned by hackers associated with Russia during the 2016 elections, according to a U.S. Senate Select Committee on Intelligence report. The report also found that the bad actors would have been able to delete voters from the rolls and manipulate data, though they didn’t find any evidence of that happening.
Some states are upgrading their systems, while others are once again turning to paper in order to have backups on-hand. Others are installing digital backup protocols so there are extra copies of the list in case anything is deleted or manipulated. Altogether, 29 states will use funds to work on registration systems.
In Rhode Island, the secretary of state is considering using $1.5 million to upgrade and centralize its voting system, and another $600,000 to come up with data recovery practices.
Florida is earmarking $1,750,000 to implement “security enhancements to the state voter registration system, contract a team of cybersecurity specialists to provide support to the state and county supervisor of elections offices, and to fund a voter education campaign to educate voters on how to get ready to register and vote in an election.”
North Carolina and Oklahoma, meanwhile, are using funds to make it easier to register to vote at the Department of Motor Vehicles and to quick change addresses online.
Election Auditing
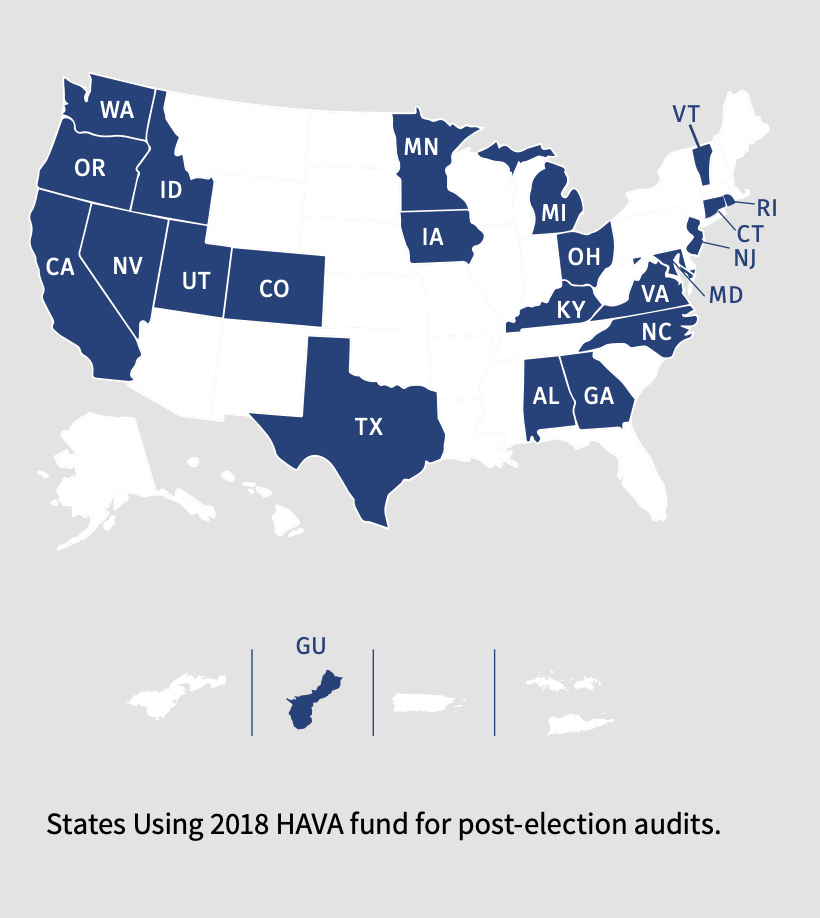
About 22 states and Washington, D.C., currently conduct post-election audits of paper ballots before they officially declare the results of elections, a practice that experts agree is vital to election integrity.
In their filings, 24 states allocated some money to either creating or increasing the efficiency of auditing, but in total only 5.6% of funds will go to the cause.
The gold standard of these protections are referred to as risk-limiting audits, which go through voting systems to ensure that there were no bugs or hacks during voting. Only two states currently require them: Rhode Island and Colorado.
New York, Connecticut, and Alabama, however, indicated that they would spend money to increase their risk-limiting audits in the upcoming election. New York is paying nearly $2 million to accounting firm Grant Thornton to “conduct a uniform comprehensive risk assessment of every county board of elections” ahead of 2020.
“Instituting risk-limiting audits is probably the most important bandaid we have,” said Sebes. “We’ve got voting systems that are so fundamentally insecure that we cannot trust them to get every vote right and make sure that when they report the election winners they’re correct.”
The current voting system in the U.S. is “patch and pray” ahead of 2020, said Miller.
“That’s the state of the state here, patch and pray and brace for impact,” and an important part of that patching is making sure voting results are actually correct. “The one thing that we think can happen is a concerted and concerned effort to see if we can get risk-limiting audits performed in at least some small fashion. The least we can do in the presidential election is make sure we’re actually capturing voter intent, especially where elections are close.”
Communication
The state of Oregon proposed spending $220,000 on a new system that would allow voters to track their ballots and “help to build trust and confidence in our election systems.” Voters will be able to subscribe to receive updates on where exactly their ballot is, “from mailing outbound to received and accepted at the county elections office.” They’ll even be able to receive text message alerts.
Other states, like Florida, will spend money on educating potential voters on how to get to the polls, though they did not specify how much.
But the experts at OSET say money might be better spent on public relations plans.
“Trust is what is at risk here, if you want your constituents to trust the election and what you’re doing you need to be transparent and communicate what you’re doing,” said Miller.
A large part of potential foreign interference has little to do with anything actually happening, said Sebes, but instead with creating distrust and discrediting the election system through social media posts and other forms of disinformation.
“Cybersecurity incidents may happen, but there may also be claims of nonexistent cybersecurity attacks. It is the election official’s job to be able to stand up against this global multi-pronged type of attack and say ‘no I’ve got my election under control, and here are the reasons why you can trust why we know who won.’ That takes lots of preparation, but it’s feasible.”













