Most of us have by now received new credit cards in the mail embedded with Europay-MasterCard-Visa (EMV) chips. Merchants across the country have been hastily investing large amounts of money in new EMV-compliant terminals.
This is because today marks the moment that retailers become liable for fraud that occurs in their stores if they haven’t upgraded their old credit card readers to the new payments standard – an inducement intended to hurry along the transition. This shift is commonly thought to be speeding us toward a more secure and less fraudulent future. But who really benefits – and who bears the costs – of this step in the transition to a cashless society is not as clear cut as it seems.
‘Chip and PIN’ comes to America
EMV, also known as “chip and PIN,” is a standard for payment cards and terminals in which the data are stored on integrated circuits (the chip) rather than on a magnetic stripe. A personal identification number (PIN) is used to verify payment, rather than a signature. With compatible terminals, they also allow contactless payments (through so-called near-field communication), which require no authentication up to a certain monetary limit.
The technology is not new. France was one of the earliest adopters of the standard way back in 1992 and since then, over 200 countries have joined in. The U.S. has been very late to the party, but it’s finally making the switch. A key milestone in this transition is occurring today: the liability shift.
From today onward, the liability for fraud committed at the point of sale on a non-EMV compliant terminal will no longer be borne by the card issuer but, instead, by the merchant. One estimate puts the total cost for the EMV rollout at $8.65 billion. The very strong financial incentive of shifted liability is why merchants are willing to adopt the terminals at such great expense.
An imperfect security upgrade
EMV-enabled payments are supposed to reduce fraud due to certain security features. They do away with the signature-based method of authentication in favor of a PIN code. The merchants do not retain the PIN entered at the point of sale by the consumer. They use cryptographic algorithms to authenticate the cardholder and transaction.
As with any security system, EMV is a long way from perfect. A number of different ways to hack EMV have been known for some time. Researchers at the University of Cambridge, for example, have shown that the card-reader terminals can be hacked to accept any PIN the criminal inputs. In a practice called ATM-skimming, thieves can install a fake PIN pad on an ATM to trick consumers into providing card information, including their PIN, which can then be used to commit fraud.
The near-field communications feature allows card users to pay by tapping their card against a reader. The unencrypted card number and expiry date, which emit from the chip, can be intercepted with a remote RFID device and subsequently used to commit fraud. It’s a bit like pick-pocketing in the digital age. Given the enormous cost of this transition, and the imperfect security of EMV, we need to ask: how large are the benefits from EMV in terms of curbing fraud?
A race to the bottom
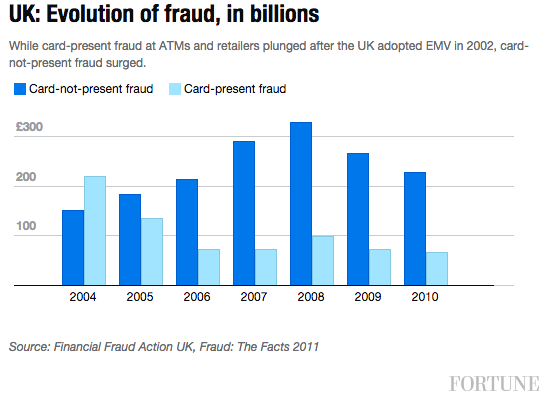
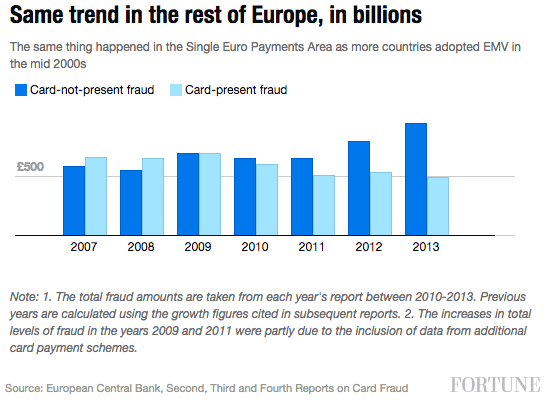
Evidence from other countries suggests that card-present fraud (face-to-face transactions) goes down following EMV adoption, as the charts below on the U.K. and the Single Euro Payments Area (SEPA) show.
However, the graphs also show a “race to the bottom” as fraudsters migrate to cross-border and “card-not-present” fraud (via the internet, phone or mail), considered much easier because EMV’s security measures, like entering a PIN, don’t work online. For an idea of the scale, in the SEPA, 66% of all fraud resulted from card-not-present payments in 2013, compared with just 46% in 2008. This broad pattern has been repeated in almost all developed EMV markets, including Australia and Canada.
So if EMV has proven to be an imperfect standard and merely migrates fraud from one category to another, why then push to adopt it at such an enormous cost?
Who gains from EMV
Card issuers and banks will benefit from a likely drop in card-present fraud of 15% to 35% over the next three years if the pattern of declines in other countries following the switch holds. Considering that such fraud was $2.2 billion in 2012, savings could be $342 million to $797 million a year.
This may be offset by the shift in fraud to card-not-present payments, which increased 40% to 100% in the three years following EMV implementation in Australia, Canada and the U.K. Such fraud in the U.S. was $1.6 billion in 2012, so we could see anything from $624 million to $1.6 billion more in the next few years. Given that the fraud is simply reallocated from card-present transactions though, a lower-bound estimate of $624 million is the more likely outcome.
Who will pay the price for this increased card-not-present fraud? The onus is on the card issuer or bank to prove that the merchant did not take the necessary measures to secure the transaction. But to meet this standard, merchants will have to implement an additional layer of security, at an indirect cost to sales, provided by the payment service providers, called a 3D Secure protocol program. If a fraudulent card-not-present transaction gets through that, the issuer or bank carries the liability. For all the billions of dollars in additional security investment, overall fraud levels will likely remain pretty stable. So why are we doing it?
The fraud sideshow
A deeper look reveals an interesting aspect to the card payments industry. For all the attention paid to rising fraud losses borne by banks, it turns out we already cover the cost, as consumers, with or without EMV. An “interchange fee” is imposed on every transaction that takes place with a card, typically 1% to 2%, and is used to cover fraud losses, reward programs and other processing costs. Merchants pay the fee, but typically pass it on to consumers in the form of higher prices.
A rough estimate places total interchange fee revenue at $45 billion to $90 billion in the U.S. in 2012 (based on the $4.5 trillion in debit, credit and prepaid card transactions that year). For comparison, total fraud, across all categories, in the U.S. was $6.4 billion – about a tenth of the fee revenue. So why are merchants (in effect consumers) paying billions of dollars to shift to a new card standard when they are already forking over tens of billions to issuers and banks to cover the costs of fraud? Add to that, the total amount of fraud following EMV basically stays the same.
It’s particularly odd, given the operating margins of MasterCard and Visa hover around 54% and 65% respectively, suggesting they have plenty of breathing room to make this hefty investment in fraud-prevention themselves. In other countries, interchange fees were cut to encourage merchants to adopt EMV terminals. But thus far, this doesn’t appear to be happening in the U.S. And since two companies, Visa and MasterCard, control 75% of the market, there’s little incentive for them to cut this lucrative revenue stream.
Questions for our brave new digital world
While the convenience of technological advances like electronic payments, and security from standards like EMV, cannot be denied, it’s important that we give thought – and are properly informed of – the price that we pay. The upgrade to EMV and its touted benefits, including reduced fraud, are not as compelling as we’re led to believe. In the end, the cost for this upgrade is being footed by merchants and, ultimately, consumers, through opaque fees and higher prices, while the limited benefits accrue to the card issuers and banks.
The EMV transition costs – and the interchange fee – hint at the problem of information asymmetry – banks and card issuers know more than we do – which allows one party to take advantage of the other. This information asymmetry is typical of the complex and bewildering technical changes that, ironically, characterize the “information age.”
So when you’re at the cash register, about to slip your chip-enable card into the new reader, think about the costs and benefits of this new technology and ask yourself: is it worth it?![]()
Benjamin Dean is a fellow for internet governance and cyber-security at Columbia University. This article originally appeared on The Conversation.