Nearly all software applications written in Java, one of the world’s most popular programming languages, contain code that has at least one known security hole, according to a new report from Veracode, a 10-year-old software security firm based in Burlington, Mass.
The vulnerabilities, which vary in severity from mild to critical, affect 97% of Java applications by way of their component parts, the fundamental building blocks of the software, the report said. Components are foundational, atomic bits of code that programmers deploy when developing more complex software, like web apps and tools for big data-processing.
Get Data Sheet, Fortune’s technology newsletter.
Chris Wysopal, co-founder and chief technology officer of Veracode, highlighted the risk these flaws pose to open source and other software projects, where code is often shared and reused.
“We can’t have a Heartbleed all over again where we’re all vulnerable to the same flaw and it’s a mad scramble,” he told Fortune, referring to a high-profile flaw in OpenSSL, a code library used to help secure internet traffic, which had information security pros panicking when it was discovered two years ago. “We can’t fix it all instantly.”
Java has never enjoyed a spectacular reputation for its security. The software, first developed by Sun Microsystems in 1995 and maintained today by the database giant Oracle (ORCL), has long been subject to attacks and frequent patching updates.
For more on Oracle, watch Fortune’s video:
There’s a danger in code components being reused throughout many applications without developers necessarily realizing it, Wysopal said. “A lot of risk is inherited, and people don’t know, because it’s two steps removed.”
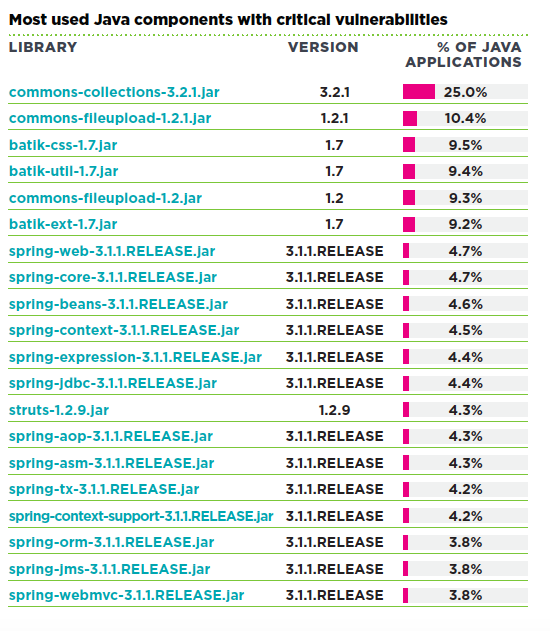
One critical flaw, a “deserialization” vulnerability that surfaced last year in an Apache code library that allowed attackers to completely take over affected computer servers, made its way into a quarter of the apps developers created that Veracode scanned. The researchers based their analysis on roughly 338,000 assessments of software applications, submitted for review by companies, open source software developers, and other parties between Oct. 1, 2014 to March 31, 2015.
Here’s a rundown of the most common severe bugs in Java components, per the report.
Another finding in the report: developers inside companies are getting better at building more secure applications internally. Veracode researchers compared the “pass rate” of apps these developers authored—testing them against an industry benchmark (OWASP’s top 10 vulnerabilities)—and found that 39% of the apps passed versus 37% last year.
Troublingly though, third-party software vendors are getting worse, the report found. Software purchased from vendors passed the same test only 25% of the time, slipping from 28% last year.
Health care is by far the worst industry when it comes to patching known problems, the report also found. Computer security pros in the field on average fix only about a third of the flaws reported to them. On the other hand, those in manufacturing, the industry that most reliably addressed software vulnerabilities, on average patched about two-thirds of the flaws after learning about them.
“That should be scary,” Wysopal said. “Almost anything health care-related you would think would have sensitive data in it.”
The most common issues affecting health care systems involved cryptographic and information leakage issues, a potentially problematic finding given the strict privacy regulations placed on health care data.