Just as the Yahoo CEO Marissa Mayer was triumphantly navigating the firm into the later stages of its promising deal with Verizon, a series of October surprises has shifted her attention. This week’s media frenzy around Yahoo’s apparent U.S. government-triggered email scanning is the latest corporate witch-hunt, and it arrives just in time for Halloween fun. Sadly, the sanctimonious denunciations it’s elicited from the usual ensemble of privacy, human rights, and technology advocates reveal a disregard for justice, facts, and reasoning that parallels that of the 17th century’s tragic Salem Village trials.
Sure, Mayer had some disappointments as the ninth CEO to run this 20-year-old enterprise, but the twin priorities of immediate performance and long-term strategic disposition have been addressed. With a billion active monthly users, 600 million unique monthly visitors, and 225 million email users, Yahoo’s resurgence has been noteworthy. In fact, revenues were up 8% over last year to roughly $5 billion, with $1.5 billion in its mobile business—up from near zero—and $1 billion in profit.
But these achievements faded into the background when, on September 22, Yahoo (YHOO) announced a massive security breach of 500 million email accounts, apparently perpetrated by Russian state-sponsored hackers two years ago.
And now this week, a separate cyber security scandal has erupted over Yahoo’s presumed compliance with an NSA government demand to scan emails. Perhaps because he lacked proper government security clearance, Yahoo’s own head of cyber security reportedly did not know about this government collaboration. According to Reuters, Yahoo’s own security team only discovered the installed software while testing Yahoo’s systems for vulnerabilities, and presumed it had been inserted by hackers.
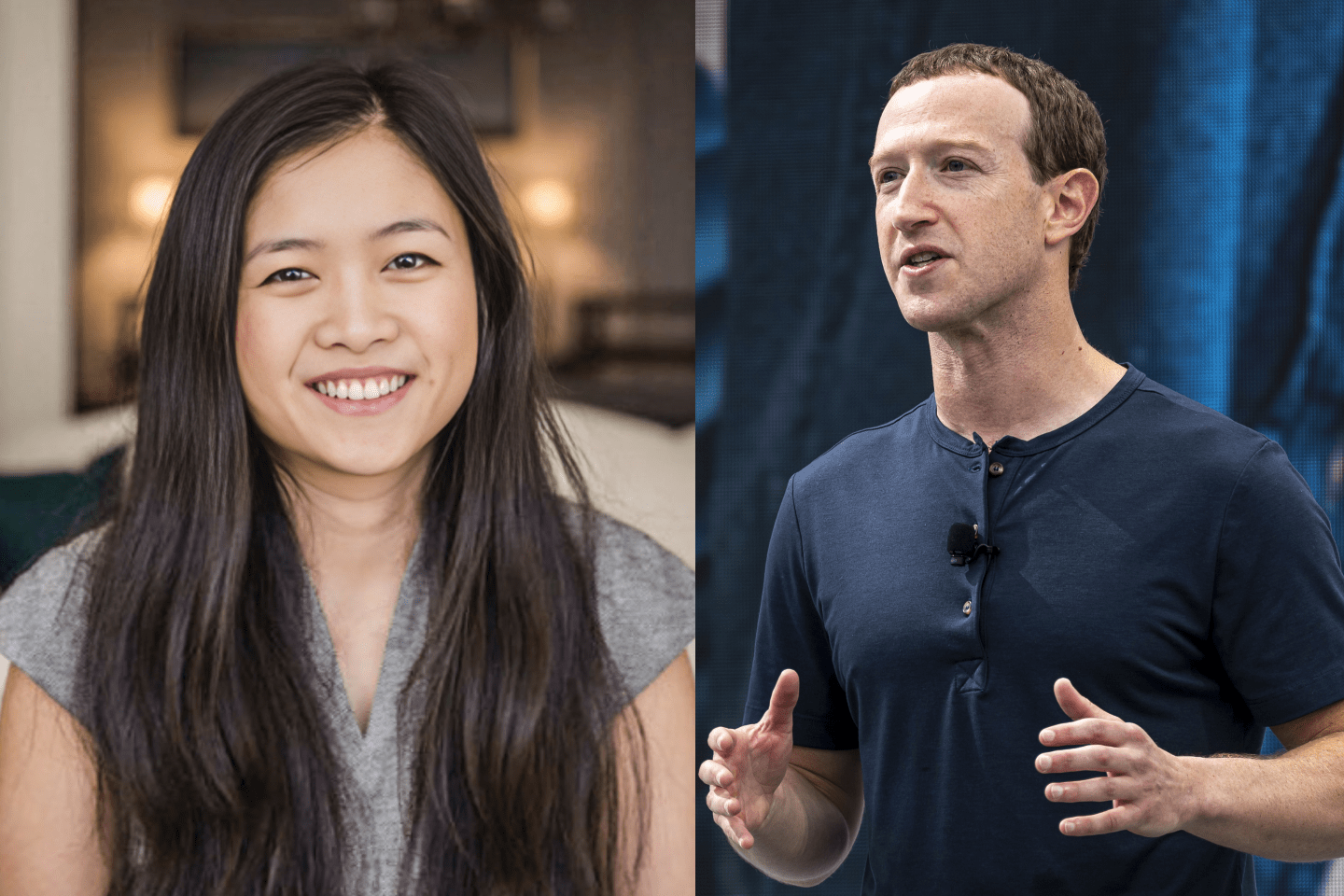
Suspiciously, the Reuters sources were three former employees, apparently including Yahoo’s former chief information security office (CISO) Alex Stamos, who now holds the same position at Facebook (FB). Interestingly, it was under Stamos’s watchful eyes that the original massive email hack attack occurred and was originally under-appreciated. In fact, while Stamos was still on the job, the internal investigation did not see any material risk to report as a new factor in the $4.8 billion tie-up with Verizon (VZ).
I consulted with a half dozen globally renowned electronic privacy and cyber security experts last night, and while they all expressed great admiration for Stamos, they also said that this move smacked of a possible defensive maneuver and diversionary effort given his own apparent professional slip-up at Yahoo. Any expert, any professional, or any great enterprise can have a bad day; reputations are not shields from accidental missteps. The renowned Stamos may well have missed the depth of the original problem.
Furthermore, cyber security experts tell me that it is inconceivable that competitor email providers were not similarly approached. In fact, the cautious denials made by Yahoo’s competitors in recent days merely captured Reuters’ overstatement of the government demands, allowing competitors to publicly cloud over their own possible limited cooperation with what was not a typical scanning process.
The explanation offered—apparently by Stamos and his defenders—was that Mayer had starved the company’s cyber security efforts. But this does seem to be a matter of fact. Indeed, insiders claim that the function actually doubled in staffing, systems, and budget under Stamos and during Mayer’s leadership.
Furthermore, Reuters was apparently inaccurate when it reported that, “When Stamos found out that Mayer had authorized the program, he resigned as chief information security officer and told his subordinates that he had been left out of a decision that hurt users’ security, the sources said.” In reality, it seems that Stamos did not immediately storm out in moral outrage, but rather remained on the job for three or four months until he got a better offer from Facebook.
Sure, there are Fourth Amendment legal search debates challenging the constitutionality of certain enforcement actions taken under the Foreign Intelligence Surveillance Act (FISA), but in this case the government demands may be far more focused than initially believed. It is hardly similar to the NSA demands upon Apple, in which it asked the computing giant to create something new. As Fortune reported, quoting top officials involved, “[T]he nature of the order did not require the company to design a program to comply with the request. Rather, the company was able to employ existing tools to execute the request.” In addition, the New York Times cited government officials stating that the specific scanning was for a particular digital signature related to foreign state-sponsored hackers to ferret out terrorists.
Not only was this parallel to commonly applauded protocols, but also the request was far more targeted than the suggestive report from Reuters. Fortune quotes a top official: “Any information that may have been provided, would have been limited to material associated with the organization’s digital signature.” These digital signatures are ephemeral, so such a targeted scan for identification and tracking would have thus been a brief passing task in a short window.
Most disturbingly, the Reuters report described the Yahoo scanning as “the first case to surface of a U.S. Internet company agreeing to an intelligence agency’s request by searching all arriving messages, as opposed to examining stored messages or scanning a small number of accounts in real time.” Huh? Yahoo and its competitors already have such protective procedures operating, and this is fully in the public interest. Such virtually identical email scanning is routinely and eagerly employed by email providers for such vital protective functions as ad blocking, viral and malware detection, and child porn eradication.
The real questions are: On whose behalf is the scanning done? Is the email envelope content actually opened? Who looks at it if it is opened? Does the scanning company have the legal right and moral obligation to do something about such abuses?
Reported efforts by Verizon to knock $1 billion of the $4.8 billion price it agreed to pay for Yahoo in light of the recent “scandals” remind us of how public and media misconceptions can have secondary, unjust financial consequences. This is why the new disclosures deserve some perspective anchored in actual facts, not inflammatory impulses on a hot-button topic like privacy. Let’s leave the witch trials to Halloween and history.
Jeffrey Sonnenfeld is Senior Associate Dean for Leadership Studies and Lester Crown Professor of Management Practice at the Yale School of Management as well as author of Firing Back: How CEOs Rebound From Career Disasters(Harvard Business School Press).