If you were affected by the latest global cyber attack that locked businesses out of their computer systems, here’s a tip: Don’t pay the Bitcoin ransom. You’ll be sorry if you do.
Beginning in Ukraine and quickly spreading to large multinational corporations ranging from Maersk to Merck, the ransomware wave has caused incredible disruption and ground operations in affected organizations to a halt. The extortionists have demanded a payment of $300 in Bitcoin in order for victims to regain access to their systems.
“We guarantee that you can recover all your files safely and easily,” the ransom note reads.
There’s a problem though. People who pay the Bitcoin fee associated with the attack—which security researchers have dubbed Petya, NotPetya, ExPetr, Nyetya, and other variations on that theme—should not expect to recover their files even if they do pay. So much for that guarantee.
Get Data Sheet, Fortune’s technology newsletter.
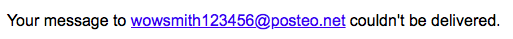
The ransom note requests that victims, after paying, provide their Bitcoin wallet ID and another identifying detail (a unique “personal installation key,” which the attackers provide). The attackers advise affected people to send this information to a certain email address: wowsmith123456@posteo.net.
As Fortune noted on Tuesday, Posteo, the email service used by the attackers quickly suspended the attackers’ account, leaving them unable to communicate with their victims and preventing them from sending along decryption keys. This means there’s no obvious way for victims to get a decryption key from the supposed extortionists, even if they do pay.
Fortune’s own note to the email address bounced back, as seen in the screenshot below.
Some security researchers have questioned whether this attack can even be properly categorized as ransomware. Matthieu Suiche, CEO and founder of the Dubai-based cybersecurity firm Comae, told Fortune that he believes it is more appropriately considered as “wiper” malware, meaning malicious software that intends to destroy data rather than hold it hostage.
Other experts have agreed with the essence of Suiche’s analysis. “Despite its presentation as ransomware, ExPetr ultimately functions as a wiper since we have discovered that the attacker doesn’t have the ability to decrypt the files even when receiving the payment,” a spokesperson for Kaspersky Lab told Fortune in an email.
Raj Samani, chief scientist at Intel (INTC) spinout McAfee, concurred. “We always recommend for ransomware victims to not pay,” he said. “In the case of WannaCry and the Petya ransom demands it’s even more advisable since the likelihood of receiving decryption keys are almost nil.”
Better put that $300 toward something more useful, like replenishing the office’s IT procurement fund.












