The Tor network—used by activists, journalists, law enforcement, and yes, criminals—is famous for cloaking web surfers’ identities and locations. And, apparently, it contains a vulnerability that poses a risk to all that protective anonymity, according to researchers at MIT and the Qatar Computing Research Institute (QCRI).
The good (or bad) news—depending on how you view Tor— is they say they’ve also come up with a fix to the problem that they will demonstrate at the Usenix Security Symposium next month, according to an MIT News story “Shoring up Tor.”
An estimated 2.5 million people—including journalists, political activists, terrorists or just consumers who don’t want to share their browsing histories with Facebook or other commercial entities—use Tor daily. And that is why the network is of keen interest not only to “repressive” regimes like Russia and Iran but to governments a lot closer to home, including our own. Not to put too fine a point on this, but one person’s activist could be another person’s terrorist, but I digress.
DigitalTrends has a good description of the Tor basics:
Tor works by anonymizing the transport of your data. Like an onion, Tor encrypts the data you send through the web in multiple layers. Your data is then “relayed” through other computers. Each relay sheds one layer then finally arrives at the source in full form. The software bounces users around a network of open connections run by volunteers all over the globe. This prevents people from spying on your Internet connection and discovering sites you visit. Tor scrambles information that could pinpoint your exact physical location.
By using a Tor-configured browser, the user enters her request, and it is automatically swaddled in those encryption layers and is sent it to the next, randomly chosen machine that runs Tor. This machine, called “the guard,” peels off the first encryption layer and forwards the still-masked request on until it finally reaches a randomly chosen “exit” machine that strips off the final layer encryption to reveal the destination.
Only the guard machine knows the sender and only the exit machine knows the requested site; no single computer knows both.
The network also offers “hidden services” that enable an activist to aggregate sensitive news reports and make them available to select users, but not the world at large. That is, the archive is not searchable or available on the public Internet.
The creation of those collection points, which involves the building of what Tor calls a “circuit” of machines, offered the researchers a way to snoop on Tor. By connecting a ton of their own machines to the network and then analyzing traffic, they were able to identify likely guard machines.
From the MIT report:
The researchers showed that simply by looking for patterns in the number of packets passing in each direction through a guard, machine-learning algorithms could, with 99 percent accuracy, determine whether the circuit was an ordinary Web-browsing circuit, an introduction-point circuit, or a rendezvous-point circuit. Breaking Tor’s encryption wasn’t necessary.
Furthermore, by using a Tor-enabled computer to connect to a range of different hidden services, they showed that a similar analysis of traffic patterns could identify those services with 88 percent accuracy. That means that an adversary who lucked into the position of guard for a computer hosting a hidden service, could, with 88 percent certainty, identify it as the service’s host.
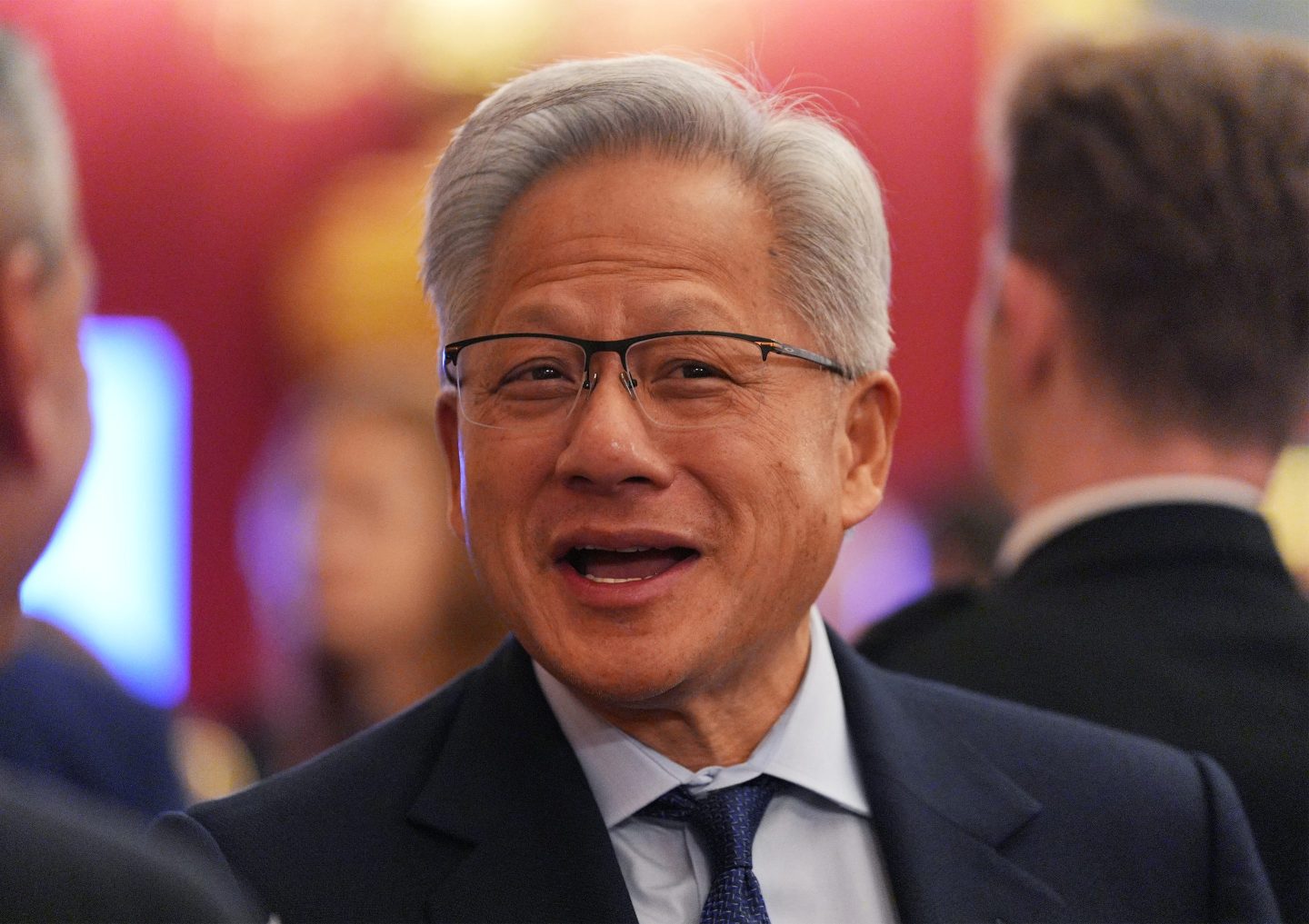
The researchers, including Albert Kwon, an MIT graduate student in electrical engineering and computer science, and Mashael AlSabah, assistant professor of computer science at Qatar University, and a QCRI researcher, said the fix lies in obscuring data traffic patterns to and from the guard machines in a way that renders such “traffic fingerprinting” ineffective.
If the network sends around enough dummy packets so that all the data sequences look the same to prying eyes, problem solved, and anonymity remains safe.
Sign up for Data Sheet, Fortune’s daily newsletter about the business of technology.