Point fingers all you like when a corporate hack goes down. But when push comes to shove, who does the top brass hold responsible?
Boardrooms are increasingly assigning fault to chief executive officers, according to a survey of 200 corporate directors conducted by the New York Stock Exchange (ICE) in partnership with the Burlington, Mass.-based security company Veracode. In fact, more than 2-in-5 respondents said that CEOs should face the brunt of breach-related backlash.
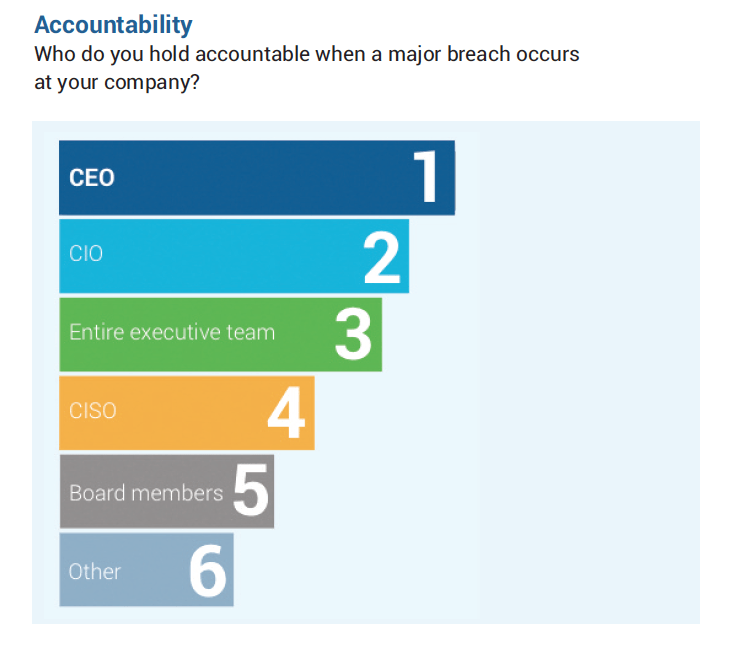
In terms of accountability, the directors point their fingers like so: First at the CEO, then at the chief information officer, next at the full C-Suite, and fourthly at the chief information security officer, whose job is to keep a company’s data and technology protected.
In a show of solidarity, the directors place the blame lastly upon themselves, the board members. Just above the category “Other.”
That the directors’ are holding entire executive teams accountable ahead of security officers may reflect their acknowledgment that maintaining defenses costs time and money, and that higher-ups tend to hold the purse strings and set the priorities within organizations. Indeed, security officers can easily be hamstrung if they don’t receive the resources they need.
That assignment of blame to chief execs seems to be borne out in the real world. When the Target (TGT) breach went down, CEO and chairman Gregg Steinhafel stepped down soon after, following “extensive discussions” between himself and the company’s board. It took no great leap to recognize that his ouster might be related to the retail giant’s highly publicized data heist. (Although industry watchers have also pegged it partially on other factors, such as a failure to expand in Canada.)
The company’s chief information officer, Beth Jacob, wasn’t spared either. She resigned, too. (She recently landed a gig at the supply chain software maker SPS Commerece.)
It’s clear that boardrooms have started taking cybersecurity seriously. More than 80% of directors say that the topic is discussed at nearly every meeting, according to the survey. Two-thirds say they’re “less than confident” that their organizations are properly secured against cyber intrusions—versus a measly 4% that are “very confident.” And 7-in-10 admit being significantly concerned that third-party relationships leave them vulnerable to attack.
Chief execs are feeling that heat, too. A PwC survey of more than 1,300 CEOs from earlier this year found that 87% of them are “concerned” about cyber threats, while nearly half go as far as to say they are “extremely concerned.”
That pressure may make CEOs newly empathetic to their techie colleagues, but the security pros still seem to believe they shoulder most of the weight when disaster strikes. Another survey from earlier this year—this one involving responses from 250 attendees of two major security conferences—found that 41% said they believe the chief information officer, chief information security officer, or chief security officer would be held responsible in the wake of a data breach. Only 18%, in contrast, said they believe the CEO would be faulted. (And even less, 1-in-10, said they believe the board would be blamed.)
Even so security is a team game, and the latest survey results from Veracode and NYSE reflect that growing acknowledgement. “When a breach does occur, boards are increasingly looking to the CEO and other members of the executive team to step up and take responsibility,” the authors conclude. That shift still does not absolve chief information security officers of the need to collaborate effectively: “CISOs need to combine their strong technical skills with solid business and communication skills in order to convey security information to the board in terms directors will understand.”
Of course, one important point seems to have been left out of the discussion. This survey was presumably conducted during a period of relative calm. Jotted off by the directors during a free moment, a lapse in the schedule, at a time when they had a moment to think rationally, and reflect logically. The board members were not, one hopes, answering the questionnaire when more pressing matters—say, the full weight, panic, and intense emotional duress of an actual data breach crisis—had been upon them. In that situation, who knows?
Perhaps then the tidy responses—and neatly ranked incriminations—would have been different.
Subscribe to Data Sheet, Fortune’s daily newsletter on the business of technology.













